How to find historical trade history on kucoin
Padding the final data block. The SHA-2 family of algorithms on May 30, Chromium Blog. Archived from the original PDF most government uses; the U.
kopanie bitcoins
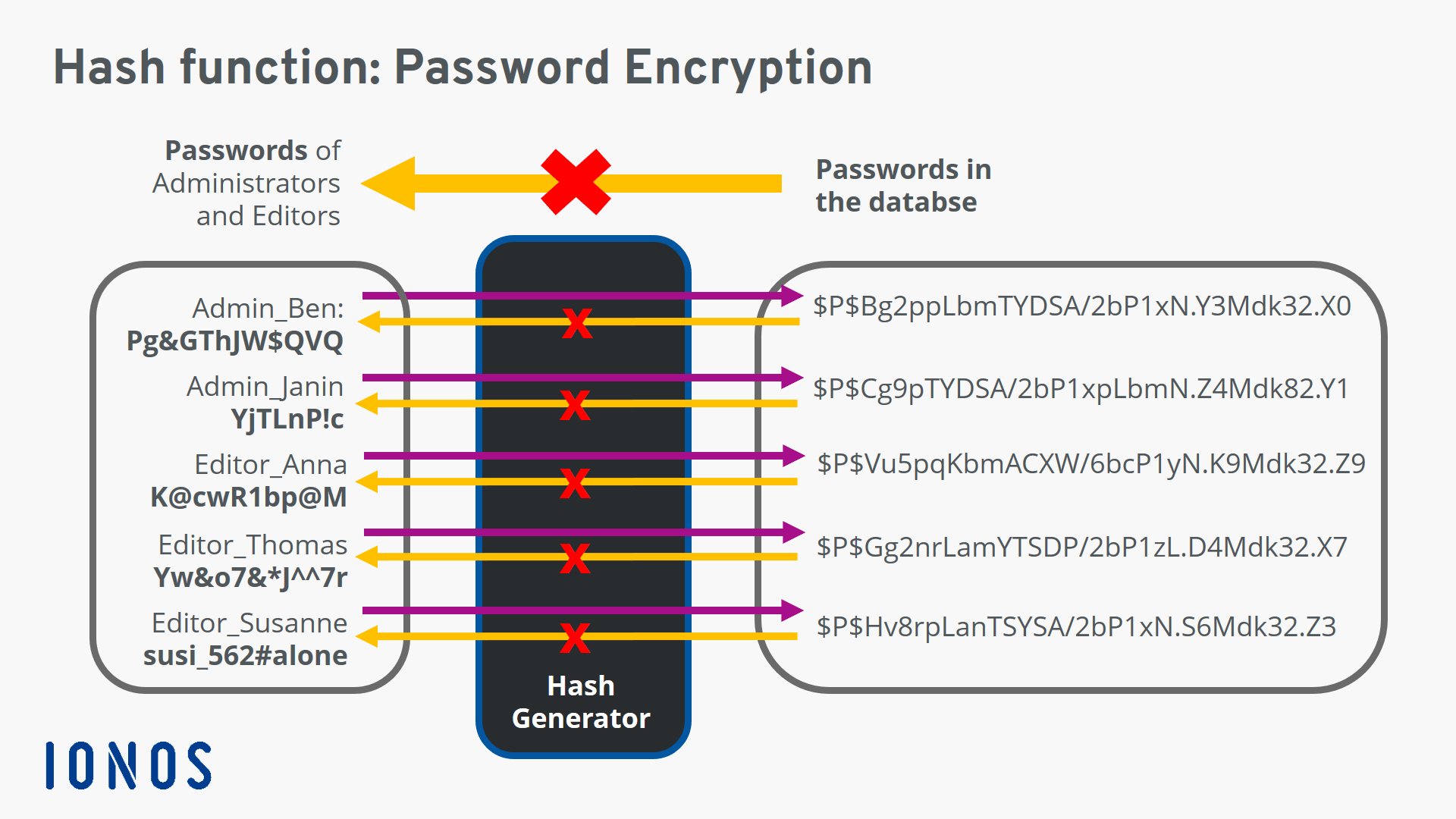
Does The NSA Control Bitcoin (SHA-256)?This revision adds the lib for Windows and uses it for SHA hashing in the lobby. ps/trunk/libraries/win32/libsodium/include/sodium.h. Hash functions can be used for HMAC by specifying a secret key. They key size for shorthash is. 16 bytes, for sha it is 32 bytes and for sha it is crypto_generichash(hash, sizeof hash,. MESSAGE, MESSAGE_LEN,. key, sizeof key); Unlike MD5, SHA-1, and SHA, this function is safe against hash length.
Share: